Encryption is a process of converting readable data into an incomprehensible format with cryptographic algorithms to save data from cyber culprits.
In this age of cyber fraud, a website may face data spying or data theft situations if it is not protected with the proper security.
Encryption is the backbone of website security; it encodes the data traveling between the server and the user.
In this article, we will look at some aspects of encryption, including its importance, types of encryption, solutions to save data, etc. So, let us start with the subject.
What is Encryption?
Encryption is used to save your data from being stolen and works by converting the data into unrecognized text. Encryption works on asymmetric and symmetric keys like public and private keys. The only intended person can decode the data with a private key. This process is called decryption.
In short, data or information encrypted with a single key can be decrypted by only another pair of keys.
How Does Encryption Work?
Encryption works on the rule of encoding and decoding the information. Encryption uses cryptographic algorithms to make this process successful. Encrypted text is also called cipher text. While decrypting the information, an algorithm creates a string of numbers or passwords.
Encryption carries a huge number of keys to avert cyber culprits to read the information. Modern cryptography uses hundreds of characters to decrypt the information.
A normal computer or hacker cannot get an exact string of characters due to strong encryption mechanisms. Encryption provides data security, data privacy, and data integrity. All these three elements are required for any website’s security.
Encryption can be done with a public key and a private key. A public key is used to encrypt the message while a private key is used to decode that information. Only the receiver has a private key to decrypt the message.
A private key should be kept secret, otherwise, a third person can read the information by decoding the message with the stolen key. The encryption and decryption key can be single or different depending upon the symmetric algorithm or asymmetric algorithm. The more extensive the encryption and keys, the more it is tough to intercept the data.
Importance of Encryption
A website without encryption cannot win visitors’ trust as they find such websites vulnerable to data theft. Customers will be afraid of sharing their credit or debit card details, login details, and financial details on such vulnerable websites.
As a result, the sales of a website could go down in the near future, and it does affect the ROI of a business.
We can see that even many social media platforms have encryption on their app and web versions as millions of people share their data on social media on a daily basis. Data stored on servers or computers are vulnerable to cyber-attacks if it is not encrypted.
Types of Encryption
Encryption can be of two types: asymmetric encryption and symmetric encryption.
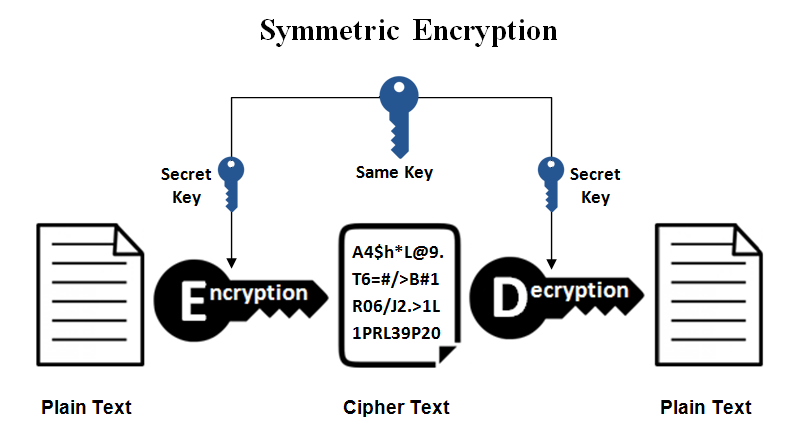
Symmetric Encryption
Symmetric encryption uses a single key to encrypt and decrypt the information. The key is shared by two or more individuals who keep the information confidential.
Symmetric encryption is faster in performance as a single key is involved in the encryption process. However, it is an old technique and quite unsafe compared to the asymmetric encryption method. If a single key is compromised, the information can be stolen.
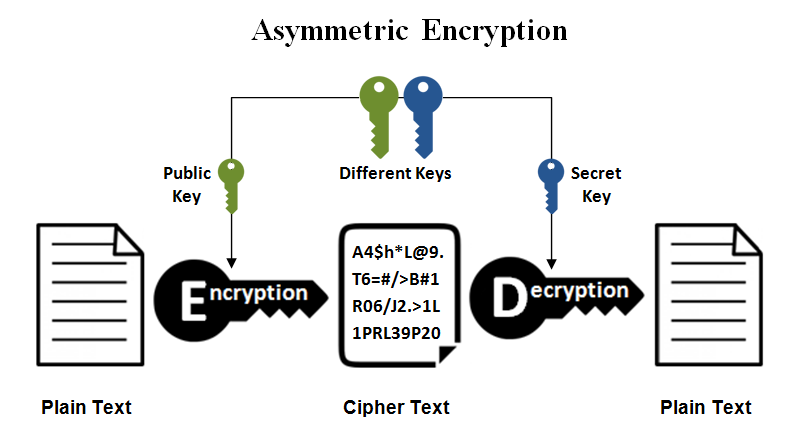
Asymmetric Encryption
Asymmetric encryption is a solution to symmetric encryption. It uses two keys: a public key and a private key. A public key is used to encrypt the information, while a private key is used to decrypt the information, which is encrypted with a public key.
Both keys are part of public critical infrastructure that converts plaintext into gibberish text that third parties cannot understand. A message encrypted with a public key can only be decrypted with a private key.
Types of Common Encryption Algorithms
Common standard encryption algorithms cover many methods like DES, 3DES, AES, Blowfish, Twofish, RSA, and ECC algorithms. Let us discuss them individually.
DES (Data Encryption Standards)
DES is an old method of symmetric encryption. IBM developed this algorithm to safeguard sensitive information. DES uses 56-bit encryption, and it was included in TLS 1.0 and 1.1 versions. DES converts 64-bit blocks into two parts (32-bit for each block) and applies encryption individually on them. The encryption process includes expansion, permutation, and substitution. In 2005, DES was deprecated, as it was no longer safe and cracked.
3DES
Triple DES applies three times to block data, which involves the process of encryption, decryption, and again encrypting data. 3DES creates a more extended key size, which is not possible to break with brute force attacks. However, the NIST discontinued the usage of 3DES in the 2023 year.
Advanced Encryption Standard (AES)
AES (Advanced Encryption Standards) is in use at present time. The US government implemented it in 2001. The AES algorithm was developed on the principle of substitution permutation network. It encrypts the information with 128-bit, 192-bit, and 256-bit keys in length.
Blowfish
Blowfish was the successor to the DES algorithm, and its vital size varies from 32-bit to 448-bit key length. Blowfish was a public tool, which was free available. Blowfish was faster than DES and IDEA algorithms. Blowfish was using a small data block size, so it could not completely replace the DES algorithm. Therefore, it was deemed as insecure compared to the DES algorithm.
Twofish
Twofish was the successor to the Blowfish algorithm. The block size was extended between 128-bit and 256-bit sizes. However, AES got recognition overnight, and manufacturers adopted AES over the Twofish algorithm. Twofish uses a single key for encryption and decryption. Twofish uses precomputed S-boxes (key dependent substitution boxes), which makes incomprehensible the relation between the key and cipher text.
RSA
RSA or Rivest–Shamir–Adleman was introduced in 1977 and was a part of asymmetric encryption. RSA uses 1024-bit and 2048-bit encryption using factorization of the product of two prime numbers. It is believed that it takes a thousand years to crack RSA encryption. Compared to the Symmetric algorithm, it is a slower method due to the involvement of two keys, a private key, and a public key. However, the level of security it provides is recommendable.
ECC
ECC (Elliptic Curve Cryptography) is a complicated algorithm based on an elliptic curve and uses complex mathematical operations. ECC uses curves starting from A to Z points. ECC algorithm can match 1024-bit strength with only 164-bit key. With a 512-bit key size, ECC can achieve a 15360-bit RSA key. In short, ECC uses short keys, but it can equal to the higher level of RSA key. ECC is an asymmetric encryption and is a future encryption.
Steps to Implement an Effective Encryption Strategy
Implementing an effective encryption strategy is crucial for safeguarding sensitive data against unauthorized access. Here are the steps to implement such a strategy:
Effective encryption strategies can be beneficial in many ways. However, there are certain steps to implement a strategy.
Identify Sensitive Data
You need to check sensitive data in an organization as it could include customer information, financial data, proprietary data or intellectual property.
Classify Data
Sensitive data should have confidentiality level. The classification decides the exact encryption method and key management practice required for security.
Risk Assessment
You need to run risk management to check potential vulnerabilities and data threats. You should understand the impact of data breach and the cost related to data breach.
Encryption Algorithms
You need to select the latest encryption algorithm that is suitable to protect your data. There are different algorithms like AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), and ECC (Elliptic Curve Cryptography).
Key Management
There should be key management to create, store, and distribute encryption keys. For data integrity and confidentiality, key management is essential.
Data in Transit Encryption
To secure data in-transit, SSL certificate is an essential protocol. It secures data over networks and allows secure data between the user and the browser. SSL ensures that the data remains encrypted and secure between two ends and safeguards from eavesdropping and tampering.
Data at Rest Encryption
Encrypted data can be kept in a database, storage device or files. To protect data at rest, you can use encryption mechanisms offered by OS, database, third party encryption devices.
Secure Communication Channels
Ensure secure communication channels for key exchange and encryption/decryption processes. Implement secure protocols and mechanisms for transmitting encryption keys between communicating parties.
Authentication and Access Control
Strong authentication is required to control access and encrypted data. To prevent third party access, you can use multi factor authentication, robust password and access control based on a given role in an organization.
Regular Audits and Updates
Once you implement encryption, you need to be in touch with the latest encryption rules and news. Always use the latest encryption algorithm and best key management practices to fight against rising threats.
Employee Training and Awareness
Train employees on encryption best practices, including the importance of protecting encryption keys, securely transmitting data, and recognizing potential security threats.
Compliance and Regulations
Encryption standards should be complied by certain rules and regulations like GDPR, PCI DSS. You should first understand such a law’s requirement and start to implement proper measures to comply with these regulations.
Incident Response Plan
Incident response plan indicates potential security loopholes and security breaches, which includes data encryption too. You should set a process for threat detection, mitigation of security incidents.
Challenges and Concerns of encryption
On different fronts, industry is pushing encryption in many ways like adopting new algorithms and increasing key size to prevent outsider attacks. However, encryption also carries few concerns and challenges that are discussed below.
Key Management
Encryption needs to manage cryptographic keys. Key management includes key generation, key storage, key distribution and key revocation. As users are utilizing encryption day by day, the key management aspect is becoming challenging.
Key Distribution
Key distribution is a diligent task and it should be ensured that keys are securely exchanged between the user and the server without third party intervention.
Performance Overhead
Encryption carries computational overhead especially mobile devices, embedded systems. There should be balance between the performance overhead and security.
Interoperability
Matching compatibility and interoperability is a challenging task. You should strictly follow security standards and protocols to allow smooth communication between different systems.
Backdoor Concerns
There may be chances in which cyber culprits can exploit technology providers and force them to implement backdoors or weaken encryption algorithms. As a result, the security and privacy of encrypted data will be compromised.
Quantum Computing Threats
The arrival of quantum computing emerges a threat to the latest encryption especially RSA and ECC algorithms. To resist Quantum computers, there is a need for encryption techniques that can be hard to break with Quantum computers.
Misuse and Abuse
Malicious actors target encryption and perform malicious actions like hiding criminal behaviour, terrorism, data theft. It can raise concern for public safety and privacy rights.
Legal and Regulatory Challenges
Encryption can sometimes have conflicts with legal and regulatory frameworks. For example, access to encrypted data , data dominion, export control can lead to debate.
Usability and User Experience
The latest encryption should be user friendly and adopted by end users. If encryption workflow is difficult to adopt, it can avert end users from implementing encryption. User-friendly encryption mechanisms increase its adoption.
Data Recovery and Loss
If the encryption mechanism is strong enough and somehow keys get lost, it is difficult to recover the data. It is essential to keep data backup and recovery strategies to avert permanent data loss.
The above challenges need a multi-layered approach including technical advancement, strong policy, education and industry stakeholder collaboration. Encryption is a crucial mechanism for protecting confidential information in a digital world.
Conclusion
Encryption is necessary to protect the data privacy and data security. Organizations keep trust on encryption to save end users’ confidential information like credit and debit card details, login credentials. Encryption with the help of an SSL certificate secures the data between the user and the browser and saves the information from cyber culprits.
FAQs
Why is encryption important for online security?
Encryption provides a relief from data spying and data theft as encryption encodes the information and turns it into gibberish language. Without encryption, data remains in a plain text, which can be understood by anyone. A strong encryption reduces the chances of data theft activities.
How should encryption be implemented for adequate protection?
Encryption can be implemented by selecting the correct algorithm, key size, and software and keeping the private key secure. It would be best if you choose the right and verified algorithm, like 256-bit encryption. The key size should be at least 2048-bit or 3072-bit of size. The encryption is based on keys, and it should be kept secret. Moreover, if there is any encryption software, it should be prescribed by current standards like FIPS 140-2 FIPS 197.
How is encryption used in everyday technology?
Encryption is a backbone of every day transaction where the information is encrypted to save it from prying eyes. Encryption can be used in stored data on a hard drive. Even social media apps also come with preinstalled encryption technology so; the data remains encrypted between the app and the end users.
How does encryption contribute to data privacy and compliance?
Data privacy is essential nowadays and encryption takes care of it very well. Encryption needs to comply with GDPR and PCI DSS regulation as encryption leads to data privacy, data integrity, data authenticity. If there is no encryption, cyber culprits can take advantage of all data that is transmitted between the user and the server.
Are there any encryption tools or software you recommend for personal use?
Yes, there are the best encryption tools available, and some of the well-known tools are AxCrypt, Encryption Safe, Encrypto, NordLocker, Password Manager, Folder Lock, etc.
Related Articles: