Homomorphic Encryption allows you to work on data without decrypting it first, thereby eliminating the chance of data theft.
We live in a world where the focus on privacy is increasing day-by-day. The importance of encryption techniques is expanding to protect both data at rest and data in transit. But what if we tell you that password protection for stored data and SSL protection while in transit is not enough? What if we propose that the world needs a new encryption technique to achieve end-to-end encryption?
Whether you believe it or not, it is true. And a new encryption technique has also been developed to serve that purpose. That technique is known as Homomorphic Encryption. In this article, we will explain it to you in detail. Without taking any more time, let us jump straight into it to understand what we are saying.
What is Homomorphic Encryption?
Homomorphic Encryption is a method that allows you to work on data without decrypting it first. It eliminates the chance of data theft.
The computations are performed on the encrypted ciphertext, producing an encrypted result. When decrypted, the result will yield the same values as performing the computations on encrypted plain text data.
Homomorphic Encryption permits you or a third party to perform operations on encrypted data without exposing the actual values. So, anyone from your company or outside can work with the encrypted data and use it. It is not necessary to have access to or be aware of what the decrypted data contains.
Just like other encryption methods, a homomorphic cryptosystem employs a public key for data encryption. Yet, what distinguishes it from other encryption methods is its utilization of an algebraic system. This unique feature enables you or others to conduct diverse computations on encrypted data.
Practically, most homomorphic encryption methods work best with integers. They mainly use addition and multiplication for their calculations. Anyone can work with encrypted data to get an encrypted result. But understanding what it means requires decryption, and only you can do that.
Sounds fascinating, right? You may be wondering, how is it possible, and how can any form of encryption achieve that? Well, that is what you’ll learn in the next few sections.
What is the Use of Homomorphic Encryption?
We all know the importance of encryption in securing sensitive data. So, we keep it encrypted while it is stored (data at rest) and also while it’s being sent from one device to another (data in transit). At least all enterprises conscious about the security of their customers do that. And most of the time, it also works well. That’s because modern encryption standards are virtually unbreakable. They require a tremendous amount of processing power and time to break through. Even trial-and-error based attacks (i.e., brute-forcing) remain futile in today’s era.
However, there is a limitation in all encryption systems: you can not work on encrypted data! If you want to perform any computations, you must decrypt it first. And when you have decrypted it, that’s the moment when someone can steal it. That someone may be one of your employees or any other hacker from outside your organization. Someone who has managed to infect your systems that process the decrypted data.
Homomorphic Encryption aims to solve this problem. It eliminates the need to decrypt data before use. While processing the data in use it ensures data security and privacy.
The Origins of Homomorphic Cryptosystems
The history of Homomorphic Cryptosystems dates to the end of the last decade. In 2010, Craig Gentry was a graduate student supported by the National Science Foundation of the United States. He proposed a new method of encrypting data.
That method is today known as Fully Homomorphic Encryption or FHE. His initial scheme was somewhat homomorphic encryption, allowing only addition and multiplication on the ciphertext. Yet, it was possible to build circuits that could perform arbitrary computations.
Ultimately, this created a Fully Homomorphic Encryption scheme. That scheme is known as First Generation FHE.
Since then, the research and development of FHE is ongoing. Two more generations of FHE have been developed under Gentry’s guidance. The second-generation FHE came in 2012, and the third-generation FHE in 2013. It was further improved in 2014 with the release of the FHEW scheme and in 2016 with the TFHE scheme.
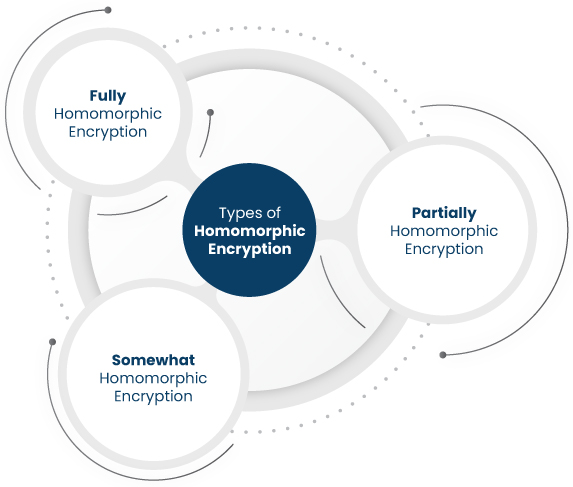
Types of Homomorphic Encryption and How it Works?
Homomorphic Encryption or HE, as it’s popularly known – comes in multiple types. And all of those types function a bit differently. However, the basic method of their function is the same.
They use an arithmetic circuit for computations instead of a boolean course used in other computing methods. Using an arithmetic circuit allows the data to be presented in an integer format instead of the plain text format. Then, the computations are performed on those integers.
That way, your employees can work on it without knowing about the actual content of the data. You’ll understand this better when we explain how three types of Homomorphic Encryption work. So let’s dive into those details now:
-
Partially Homomorphic Encryption
This type of Homomorphic Encryption carries out mathematical functions (i.e., addition, multiplication, etc.) without decrypting the data. But for other functions, you need to decrypt it first.
-
Somewhat Homomorphic Encryption
This type of encryption allows certain mathematical functions to be performed unlimited times on the encrypted data. In contrast, other functions can be performed only a fixed number of times, or up to a certain level of complexity.
-
Fully Homomorphic Encryption
As its name suggests, this type of encryption allows all functions to be performed unlimited times and up to any level of complexity without requiring the decryption of data. It is the most secure type of Homomorphic Encryption that you can get today.
With this in mind, now let’s take a little more detailed look at Fully Homomorphic Encryption (FHE).
What is Fully Homomorphic Encryption?
We have already explained what fully homomorphic encryption is concisely. Now, let’s see how it works with the help of an example.
Suppose you run a company that lends money based on people’s credit history and financial standing. You need to check their income during a fiscal year and their credit score to determine whether they can repay the loan or not.
So, you extract their credit score from the credit bureau and ask them to submit their Income Tax Returns for the last financial year to make a decision. They bring you the data in an encrypted format, and you also store it on your systems in an encrypted form.
So far, so good. But when you need to analyze their financial standing, the data must be decrypted. And you don’t want to trust your employees with something as sensitive as your customers’ financial data. You fear they may leak it to your competitors, who may then use the data to steal your customers. So what do you do? Here is the solution:
- You extract your customer’s income and credit score in a Homomorphically encrypted format.
- You extract the total amount of their existing loans in a similarly encrypted form.
- You send this encrypted data to your employees for processing. They run it through the loan eligibility formulas and algorithms of your company. The algorithm does its job and generates a score in the predetermined range set by you. Your employees send the resulting score (which is a homomorphically encrypted result).
- You use your private key to unlock the result and see if your algorithms say the person is eligible or not for the loan.
Throughout the process, your employees do not know whose data it is, the exact income, credit score, and loan history of the individual. In fact, they don’t know the outcome of the algorithm’s computations. Only you know that, thereby eliminating all chances of data theft.
By now, you understand the potential of this revolutionary encryption method. Now, let us explore some areas where this potential can be put to use.
Where does Security of Fully Homomorphic Encryption stand?
The security of a Fully Homomorphic Encryption (FHE) is rooted in a complex mathematical problem. It is called the Ring-Learning With Errors (RLWE) problem.
This problem is closely linked to high-dimensional lattices, which are abstract mathematical structures. The difficulty of solving the RLWE problem has been extensively studied by experts in the field.
This thorough examination and the widespread affirmation of the computational difficulties of the RLWE problem lay a solid foundation for the safety of FHE systems.
FHE is at least as secure as widely used encryption techniques currently defined for security.
Simply put, FHE is a strong and safe encryption technique supported by a lot of research and academic rigor because of the mathematical intricacy of RLWE. This security is a critical factor in protecting sensitive data in practical applications.
Applications of Fully Homomorphic Encryption
FHE can turn out to be a game-changer for several applications in the computing industry. Some of its possible applications include:
Storing Sensitive Data in the Cloud
Companies often store their data in cloud environments to preserve their precious resources. However, the security of cloud servers is in the business of someone else. You can’t do much about it – or it seems so, until now.
But homomorphic encryption can change that by allowing you to save data encrypted by you to the Cloud. And you’ll still be able to search for it or perform other functions on it, without having to decrypt it first.
Analyzing Data in Banks and Other Financial Institutions
Banks and other financial institutions handle a lot of sensitive data daily. Their ability to work with data without having to uncover your financial information can be a game-changing situation for the whole financial industry.
For instance, an employee of the bank may be able to determine whether you qualify for a loan or not. That too without going through your sensitive financial information like your bank account number or the amount of money available in your account.
Electronic Voting
Homomorphic encryption can improve the voting procedures of significant democracies worldwide.
Researchers are working on special encryption schemes like the Paillier scheme. It has been designed to implement Homomorphic Encryption in the electronic voting systems. By doing so, voters can cast fair votes while maintaining their right to privacy.
Enhancing Supply Chain Integrity
Recent incidents have shown that cyberattacks can target weak points in the supply chain, leading to costly data breaches.
Homomorphic encryption steps in as a guardian of your supply chain’s security.
Imagine entrusting sensitive data to a partner for processing, like tracking products from manufacturer to delivery.
By using homomorphic encryption, all this data remains securely encrypted. Even if a breach occurs at a partner’s end, your company remains unscathed. This means you can outsource critical data processing without any risks.
Navigating Regulatory Requirements
The General Data Protection Regulation (GDPR) applies strict rules to data handling.
This is especially the case in the European Union (EU). Suppose your company operates outside the EU but deals with EU data. GDPR’s requirements can be challenging to navigate. However, when data is encrypted using homomorphic encryption, it opens up new possibilities.
Encrypted data doesn’t fall under the same geographical restrictions. This makes it easier for companies to comply without breaking a sweat.
Decoding Private Data Insights
Tech giants like Meta, formerly known as Facebook, thrive on understanding user data for targeted advertising. But, user privacy is a paramount concern. Enter homomorphic encryption, a game-changer.
This technology lets Meta perform in-depth data analysis without ever peering into your personal information. It’s like solving a puzzle without seeing the pieces. This means more private, personalized ads for users while keeping their data confidential. This proves that privacy and personalization can coexist in the digital age.
These are just some of the many possible scenarios where FHE can be applied to improve the security of data significantly. As more and more development takes place in this technology, more use cases will also emerge.
Limitations of Fully Homomorphic Encryption
You may be wondering, if FHE is so good, then why is it not being used by every organization around the globe? Why is it not the default method of encryption? Well, there are always two sides to the coin. FHE is good, but it has two severe limitations, which you can see below:
It’s Slow
The first limitation of FHE is that it’s quite slow. It’s so quiet at the moment that it can’t be put to any practical use.
The computational overhead of FHE is enormous at the moment. It refers to the time spent performing computations on the encrypted version vs. the decrypted data version.
To make FHE mainstream, IBM released the first version of its HElib C++ library in 2016. However, reports suggest that it ran 100 trillion times slower than the computations done on plain text.
If something like this is put to use in complex business environments, the computing power on the face of the earth will fall short of satisfying its requirements.
Limited Support for Multiple Users
Another shortcoming of FHE is limited support for multiple users. All FHE cryptosystems work by establishing a database that is used for computation as well as decryption of computed results.
The security of the database is dependent on the security of this database. If someone can access this database, then they can also find out the decrypted plaintext result of any computation.
Now, one way for the provider of the Homomorphic cryptosystem to ensure the security of this database is to have a separate database for every user. However, this becomes impractical for a large number of users. That’s why some researchers are working on multi-key FHE cryptosystems. But until those systems are developed, this is a significant limitation in mainstreaming the FHE.
It’s due to these limitations that FHE has not become a mainstream encryption method at the moment. However, researchers are working hard to fix both of them so FHE can become the encryption method of the future.
Implementations of Fully Homomorphic Encryption
After looking at the limitations, it is clear that practical implementation is currently not possible. But that doesn’t mean there are no implementations available.
Major tech companies like Microsoft, IBM, and Google are working hard to speed up the development of FHE. They want it to become the default method of encryption in the near future. Some of the FHE implementations already created by them include:
- Simple Encrypted Arithmetic Library (SEAL): Microsoft has created this library that can be used to allow computations directly on encrypted data.
- Private Join and Compute: This open-source tool has been developed by Google, which provides an analysis of data in an encrypted format.
- HElib C++ library: This one we’ve already discussed above. IBM released it in 2016, though it was found to be quite sluggish at the moment.
Conclusion
As of today, Fully Homomorphic Encryption schemes may have their limitations. But the researchers in the computing industry are working hard to fix that. There is no doubt that FHE is going to be the encryption standard of the future. Keep an eye on its development. As it becomes more and more practically applicable to your business, consider the option of using it at the earliest.
Related Articles: