How SSL Renewal Keeps Pace with Dynamic and Distributed Environments
Traditionally, the operating environments were relatively simpler with a fixed number of servers, stable application hosting, and a certificate inventory that did not change much. This allowed IT or security teams to manually track expiry dates, avoid missing renewal schedules, and deploy them without operational disruption.
Cut to today’s modern complex infrastructure, which is dynamic, distributed, evolving, and growing continuously. Workloads are created and removed on demand, and applications run across containers, load balancers, edge services, and more. This means SSL certificates are spread across infrastructure layers, which are in a constant state of flux.
This piece works through what that looks like in practice across cloud environments, Kubernetes clusters, containerized microservices, and multi-server deployments where certificates are no longer one team’s responsibility sitting in one place.
What is SSL certificate automation?
SSL certificate automation is the use of software tools and protocols to automatically handle the issuance, validation, installation, renewal, and revocation of SSL/TLS certificates across systems without manual intervention.
Also Read: SSL Certificate Automation: The Complete Guide to Automated SSL Renewal
Why Traditional SSL Renewal Breaks Down in Modern Environments
What was once a manageable process must now operate across short-lived workloads, dynamic scaling events, and multiple certificate touchpoints across the stack. This is why organizations increasingly need to automate SSL in cloud environments.
A few core issues explain why manual SSL renewal breaks down:
- Ephemeral workloads make manual tracking unreliable. In cloud-native environments, workloads may exist for hours rather than months — instances get replaced, rescheduled, or terminated constantly. Certificate dependencies can shift faster than any spreadsheet or runbook can keep up with.
- Auto-scaling creates infrastructure dynamically. New instances appear instantly in response to demand. But if certificate provisioning still needs a human in the loop, there’s a gap — infrastructure is ready, but trust isn’t.
- Certificates are now distributed across multiple layers. Load balancers, ingress points, reverse proxies, application services, APIs, staging, production. What used to live in one place now lives everywhere.
- Manual handling increases operational risk. A missed renewal, an incomplete deployment, or inconsistent updates across endpoints can all lead to outages, service interruptions, and avoidable incidents.
This challenge spans cloud environments, containerized platforms, and multi-server architectures — where certificates are distributed, short-lived, and no longer managed in one place. Kubernetes is one of the clearest examples of how this complexity plays out in practice.
SSL Automation in Kubernetes and Containerized Environments
Kubernetes is especially well-suited to SSL certificate automation, which is why it has become a critical operational priority. A Kubernetes environment makes manual certificate management redundant as workloads are continuously orchestrated, scaled, and replaced. This means certificates cannot be renewed and simply left in their places; these need to be issued, attached, rotated, and made available across an environment where not just workloads, but even traffic and service relationships are constantly in motion.
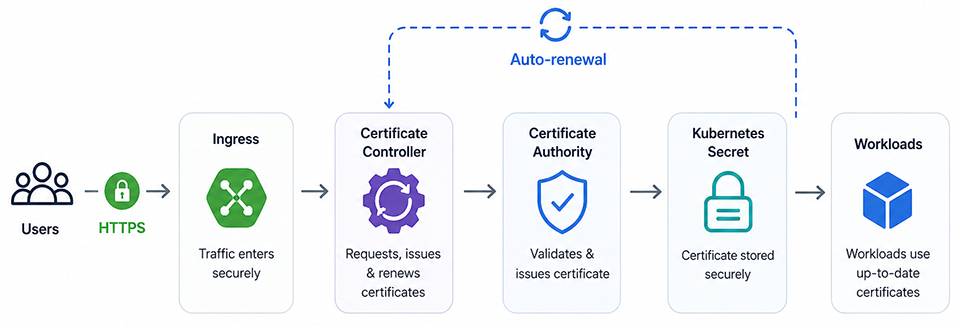
In Kubernetes, ingress controllers emerge as the most visible certificate attachment points, because their job is to manage how external traffic reaches services inside the cluster. They become a natural starting point for Kubernetes automation. But the real operational value of automation is delivered by certificate controllers, which are the automation layers within the cluster. These controllers can request, issue, renew, and update certificates based on cluster configuration and policy.
Once a certificate is issued or renewed, it must be securely rotated and propagated to the workloads or services that depend on it. In Kubernetes, that often means updating secrets and ensuring that renewed trust material is available where it needs to be. This turns automation into more than a scheduling function. It becomes a mechanism for secure and repeatable certificate movement across the cluster.
Pod-level access also matters. Some applications consume certificates directly, whether through mounted secrets, sidecars, or internal service communications. If updated certificates still require manual restarts or operational workarounds, renewal remains incomplete. Real automation reduces that friction and makes trust updates part of normal platform behavior.
Certificate issuance depends on how domain ownership is validated and in cloud environments; this is handled through ACME challenges.
ACME Challenge Types in Cloud Environments:
When using an ACME-based issuer, certificate issuance requires a domain challenge. Two types are common in cloud deployments:
- HTTP-01: Works well for standard ingress setups where the issuer can reach a public endpoint. Simpler to configure but requires HTTP access.
- DNS-01: Required for wildcard certificates and better suited for private or multi-region environments. Integrates with DNS providers like Route 53, Cloudflare, or Google Cloud DNS via cert-manager solvers.
Multi-Server Certificate Automation at Scale
Once certificate automation spans multiple servers, environments, or applications, the challenge is no longer just about renewing certificates on time. It is making sure updated certificates reach every endpoint that depends on them.
- Centralized deployment for consistent distribution
In a multi-server environment, multi-certificate automation is underpinned by centralized deployment, which is a reliable way to distribute certificates across systems, regions, and services. Without centralization, this deployment can suffer from fragmentation, with some endpoints being updated quickly while others lag behind, and the problem is further accentuated by inconsistent visibility across deployments. - Load Balancers are Key Termination Points
Load balancers often play the role of TLS termination points, making them a critical part of the certificate automation chain. The certificate renewal might be correct on the backend, but if the updated certificate is not deployed to the load balancer, users may still encounter secure connection errors or service disruption. - Reverse Proxies Need Synchronized Updates
NGINX and HAProxy are reverse proxies that sit in critical traffic paths. But deploying certificates is not enough; the proxy also needs to reload gracefully so the new certificate takes effect without dropping connections. Automation must handle both the deployment and the reload signal, ideally as a single atomic operation. - CDN and Edge Infrastructure Extending the Trust Boundary
CDN and edge environments add another layer of complexity because many organizations serve users through distributed public-facing endpoints. Certificate validity at the edge is just as important as certificate validity in the origin environment, and if automation stops short of that layer, renewal remains incomplete.
In a multi-server environment, SSL renewal automation is about achieving reliable consistency at scale. The focus should be on not missing any endpoint or traffic layer.
Automating SSL for Containers & Microservices
Certificate automation for containers and microservices is a complicated process because trust is no longer limited to the external edge. Services are constantly starting, stopping, moving, and interacting with one another, which means certificate management has to walk in step with a super-dynamic communication model.
Here are the key considerations of automating such environments:
Dynamic Service Discovery
In containerized environments, services do not always live at fixed locations. They are discovered dynamically as workloads scale, shift, or restart. That makes manual certificate management difficult, because trust relationships must adapt to changing service endpoints.
Internal Certificates
SSL automation in these environments is not only about public-facing HTTPS. Internal certificates are equally important because microservices depend on secure service-to-service communication. As the number of internal connections grows, manually issuing and updating certificates becomes difficult to sustain.
Service Mesh Considerations
In service mesh architectures, certificate management becomes part of how trust is established across the application. The mesh can automate encryption and identity across services, but that also means certificate lifecycle management must be continuous, coordinated, and built into the environment.
SSL certificate automation for containers and microservices is primarily about maintaining trusted communication across an application architecture that is constantly in motion.
SSL Automation Through DevOps and CI/CD Integration
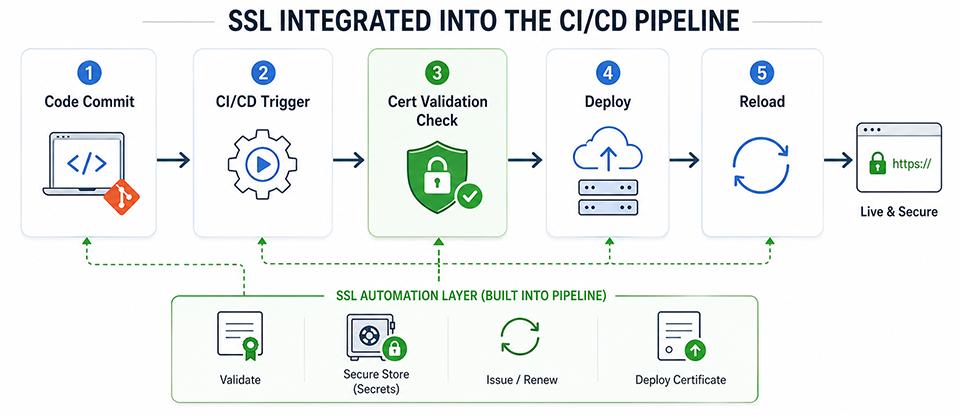
DevOps SSL automation works on the logical and proven assumption that, rather than fragmented automation, it should be integrated into delivery operations. Ideally, automation should be a part of the same workflows that govern infrastructure, deployment, and configuration; aligning with how modern systems are built and delivered through the Software Development Life Cycle.
One of the key components of DevOps automation is pipeline integration. The key elements of SSL automation such as validation, deployment checks, and certificate-related actions can be incorporated into CI/CD workflows; so that it becomes a natural checkpoint within the software release cycle. Thus, there is more synchronization between application delivery and infrastructure security.
DevOps SSL automation is further strengthened by Infrastructure as Code (IaC), which drives repeatable certificate configuration. When load balancers, ingress definitions, proxies, and related settings are declared in code, certificate dependencies become easier to manage consistently across environments.
Another critical element is secrets management. Automation speeds up certificate handling, but it shouldn’t compromise the security of private keys and certificate material. Secure storage, access control, and controlled distribution remain important, ensuring private keys and certificate materials can be accessed only through predefined permissions and injected into workflows only when needed. This allows teams to automate renewal and deployment at speed while still maintaining control over how sensitive material is handled across environments.
The broader principle is simple. Automation should fit into existing infrastructure workflows, not sit outside them. When renewal becomes part of the operational pipeline, it becomes more reliable, more visible, and easier to sustain.
To Conclude
SSL automation across complex, distributed environments is about both efficiency and resilience. Infrastructure changes quickly and widely, rendering manual processes ineffective. The real value is not only ensuring on-time certificate renewal, but also doing so through the lens of consistency, security, and reliability.
Whether you are working with Kubernetes, multi-server deployments, containerized microservices, or a mix of all three, the approach is the same: bring SSL into your operational pipeline, cover every termination point, and treat certificate management as a first-class infrastructure concern.
Related Articles:
- How ACME Is Transforming SSL Automation for Modern Enterprises
- How Automated SSL Renewal Works with ACME and Zero-Downtime Deployment