The SSL certificate is now become very important in almost all IT applications. To survive in e-commerce, a website needs to be secured with an SSL certificate. It secures transition of data on the internet and online transactions.
It will be no wonder if all the applications residing on the network start acquiring SSL certificates to secure their respective domains. In this article, you will come across the facts regarding installing and choosing the legitimate SSL certificate. This article will be helpful for someone working in Windows environment daily. It will be advantageous for those who regularly deal with a number of clients and servers having different versions of Windows installed.
Uses of SSL certificate:
The basis of usage, SSL can be categorized in three parts. They are:-
- Authentication
- Encryption (Privacy)
- Integrity
You must check which use of SSL applies to your work, also how many certificates you will need.
Let’s see the above usage of SSL in brief.
Authentication:
SSL certificates authenticate the identity of a particular applicant (individual or a business). It justifies the both the ends, the client and the server. It assures the clients that they are visiting a genuine server, secured with accredited authority.
Generally websites dealing with personal information of customers like – contact details, credit card details, passwords, bank account numbers, etc. needs to be authenticated. Any customer visiting the website should be confident about the privacy of his/her data. While providing their personal information, a customer should not feel uncertain regarding the safety of his/her data.
So, if you are handling such kind of work on your server, then you need proper authentication of your server. Learn how certificate authorities authenticate your business.
Encryption (Privacy):
For the sake of confidentiality, we want that our sensitive data is transmitted in encrypted format via the network. SSL encrypts the data transferred from the client to server and vice versa. The encrypted data will not be tampered, corrupted or modified. How does SSL support encryption of data swiftly? SSL contains a public key. Now, anybody who wishes to send information to the holder of the certificate can use the public key.
If you need to send your data to the destination and you wish that the data remains the same as desired even after reaching the destination, then the data must be encrypted. And for that you need an SSL certificate.
Integrity:
SSL offers a robust encryption that frees you from the worry of data theft so any outsider would not be able to alter or modify the encrypted information. Such amazing quality bestows data integrity that travels between the server and the browser. The data will remain secure that enhances the confidence of customers and becomes one of the reasons to drive traffic to the website.
Main Types of SSL certificate
The certificate authority issues SSL certificate, and a majority of browsers trust such certificates.
Although in functions and features, all the SSL certificates are similar. The difference between certificates is a level of trust gained by them.
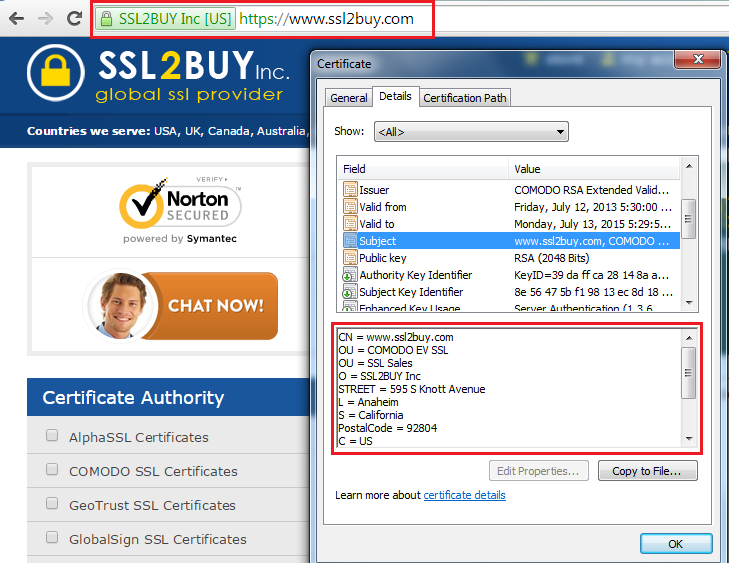
Some of the general properties that all SSL certificates include:-
- Identity of party holding certificate
- Identity of party issuing certificate
- Valid range of date
- Public Key (PK)
- Algorithm of Public Key
- CSR value
- CSR algorithm
Different types of SSL certificates are:-
- Self-signed certificate
- Standard third party certificate
- Extended validation certificate
- Code signing certificate
Each certificate gives a different proportion of verification. As the level of verification increases, the level of authentication also increases.
Self-Signed Certificates
As the name suggests itself, Self-Signed certificates are signed by the issuer itself. It means that issuer himself/herself is taking the responsibility of the assurance of his/her server.
The best part of this certificate is that it can be generated on your own that comes at free of cost. There are several tools available in the market for generating self-signed certificates like – OpenSSL package and IIS 6.0 rootkit.
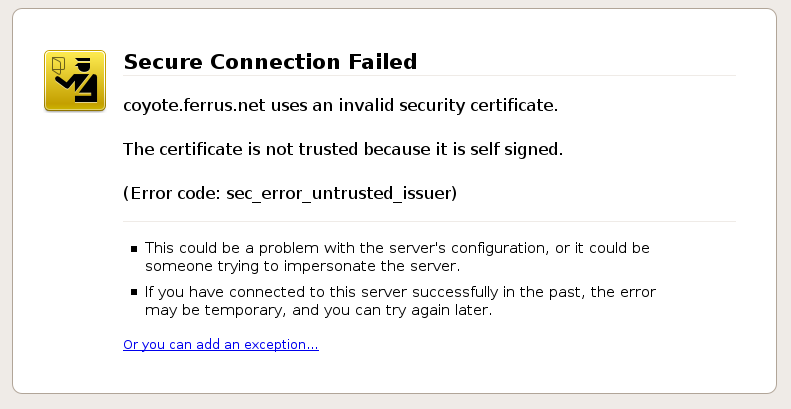
The worst part of this certificate is that it is not trusted by many users also browsers show a warning while opening such sites. For example – Mozilla Firefox shows a warning “This connection is Untrusted”. Google Chrome shows the red color on the screen to highlight the warning of unsecured connection.
Standard Third-party certificates
These are the certificates issued by the trusted and recognized third-party like CA (certificate authority). While using such type of certificate, you don’t need to be concerned about the above warning. All the browsers claim those websites are safe which have an SSL certificate issued by third-party. As a matter of fact, the browser verifies the information from OCSP and verifies the web site certificate information.
It is wishful to purchase an SSL certificate from CA certified vendors, for example – Symantec, Thawte, Comodo, AlphaSSL, GlobalSign, GeoTrust and AlphaSSL. Also, look for salient features like – mobile support, technical support, refund policy, extended warranty and so on.
Extended Validation Certificates
Web sites handling a high level of transactions are more prone to phishing attacks. Online shopping websites, online banking websites could be the main targets for cyber crimes. Hence, websites like these require a high level of security.
For obtaining an Extended Validation certificate, a website owner has to go through a deep process of verification of a business. Such certificate can be issued to those businesses who have established legal identity and physical presence of a website owner. The CA will check the authority of an applicant about its domain control. The CA will check the documents regarding legal obligations, which should be signed by an authorized officer. The identity and authority of a website owner will be checked by the CA.
EV SSL certificates are the costliest as they provide a great level of trust as well as security.
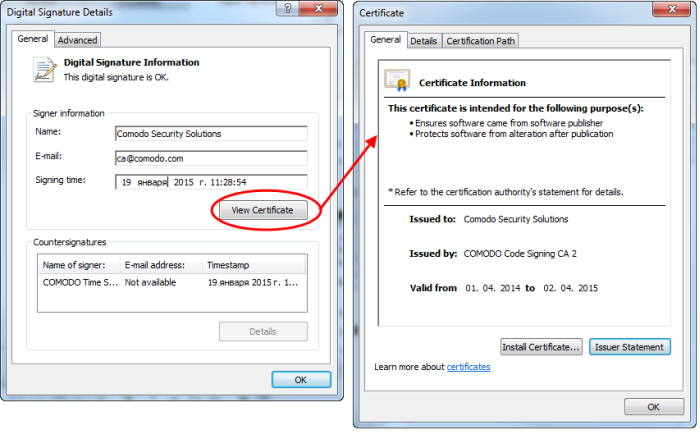
Code Signing Certificates
Code signing certificate refers to the signing of code and scripts by a certified authority to prove that the code is an original work of authorship and is not manipulated. It is signed by a cryptographic hash. Code signing is such a process in which a software developer possesses an SSL certificate from a designated authority and affiliates it with his/her application. We trust the authority that signs the SSL certificate, in the same manner we also believe that the software is trustworthy.
In order to get your code signed by certified entity, you need to purchase a code signing certificate.
How to obtain SSL certificate?
For obtaining an SSL certificate, you should first be clear about your requirements, and then you must choose the best-suited certificate.
Each SSL certificate has different levels of authentication you should choose wisely between different SSL certificates depending on your respective needs.
The following steps should be taken in consideration for obtaining SSL certificate:-
- Analyze the need of SSL certificates based on the criteria like authentication, encryption, and integrity.
- Choose from a variety of SSL products like – Standard Domain SSL, Organization Validation SSL, EV SSL, Wildcard SSL, SAN SSL certificate, etc.
- Accumulate the details required to purchase the SSL certificate such as – domain, organization details.
- Create a CSR. CSR stands for Certificate Signing Request. It is used to request the certified authority or third-party to sign the SSL certificate for you.
- Acquire the SSL certificate.
- Initialize the SSL certificate to the server.
An online sale is booming still many customers believe that online shopping is not so safe. However, if the website is secured with an SSL certificate, then there are highly chance of visitors click on your website and complete their transaction. SSL certificate helps to boost the trust in customers, hence in a long run, the overall ROI of business would increase. Most SSL certificates come with 256-bit encryption and 2048-bit CSR encryption that offers a secure environment over the web.